Plenty of bloggers have written about creating groups of health service watcher objects. The purpose of these types of groups is primarily for notification subscriptions. The reason why we need to include Health Service Watcher objects in our subscription criteria is so recipients also receive notifications about Health Service Heartbeat Failures and Computer Not Reachable alerts.
In this post, I will demonstrate how to create these type of groups using the Visual Studio Authoring Extensions.
In this example, I will create a group of health service watcher objects based on membership of another group (the "source" group). How the source group was created does not matter, as our group of Health Service Watcher objects will always be dynamic in nature and match the source group membership.
Before you start, you’ll need to locate the sealed version of the MP that contains the source group. In this case, I’ll reference a built-in group in the Windows Operating System MP: Windows Server 2012 Computer Group. To figure out which MP the group is stored in, you can run the following command in the Operations Manager Command Shell (replace with your group name).
Get-SCOMGroup -DisplayName 'Windows Server 2012 Computer Group' | Get-SCOMClass | Select ManagementPackName
In this example, the group is stored in the Microsoft.Windows.Server.Library.
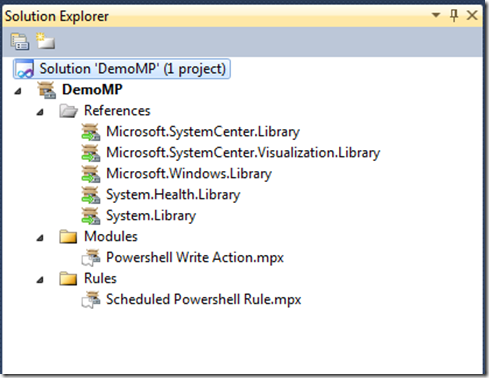
1. Create a new Operations Manager 2012 Add-On project in Visual Studio, name it Demo.HealthServiceWatcherGroups, and add a reference to the Microsoft.Windows.Server.Library MP (or the MP containing your source group). Also add a reference to the Microsoft.SystemCenter.InstanceGroup.Library MP – you need to reference this for the discovery relationship.
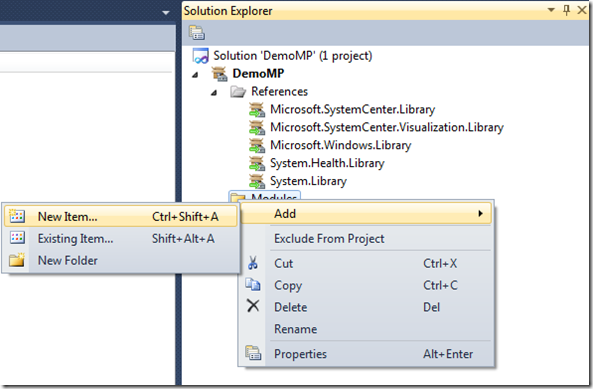
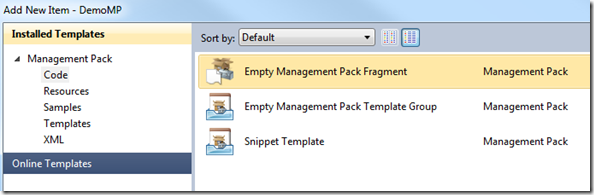
NOTE: I use fragments heavily in MP authoring, and don’t rely on the templates at all. I think it offers much more flexibility and allows me to retain a library of my own fragments that I can reuse later. This MP will consist of three fragments; one for the MP display name, one for the singleton class (group), and one for the group discovery.
2. Add a new empty management pack fragment named mp.DisplayName.mpx, paste the following code into it, and save the fragment. This fragment will provide the MP friendly name.
<ManagementPackFragment SchemaVersion="2.0" xmlns:xsd="http://www.w3.org/2001/XMLSchema">
<LanguagePacks>
<LanguagePack ID="ENU" IsDefault="true">
<DisplayStrings>
<DisplayString ElementID="Demo.HealthServiceWatcherGroups">
<Name>Demo – Health Service Watcher Groups</Name>
<Description>This management pack contains groups of Health Service Watcher objects.</Description>
</DisplayString>
</DisplayStrings>
</LanguagePack>
</LanguagePacks>
</ManagementPackFragment>
3. Add a new empty management pack fragment named class.WindowsServer2012HswGroup.mpx, paste the follow code into it, and save the fragment. This fragment provides the group name and establishes the relationship type. Notice this is a singleton class, which is a group in this case. Also note that I am using default aliases that are generated by VSAE. I choose to use default aliases all the time, so I don’t get confused with custom aliases later. My preference is to store display strings in each fragment, rather than bunching them all into a single fragment, but you might find other methods that work better for you.
<ManagementPackFragment SchemaVersion="2.0" xmlns:xsd="http://www.w3.org/2001/XMLSchema"> <TypeDefinitions> <EntityTypes> <ClassTypes> <ClassType ID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup" Abstract="false" Accessibility="Public" Base="MSIL!Microsoft.SystemCenter.InstanceGroup" Hosted="false" Singleton="true" /> </ClassTypes> <RelationshipTypes> <RelationshipType ID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroupContainmentRelationship" Abstract="false" Accessibility="Public" Base="System!System.Containment"> <Source ID="Demo.HealthServiceWatcherGroups.Source" Type="System!System.Group" /> <Target ID="Demo.HealthServiceWatcherGroups.Entity" Type="System!System.Entity" /> </RelationshipType> </RelationshipTypes> </EntityTypes> </TypeDefinitions> <LanguagePacks> <LanguagePack ID="ENU" IsDefault="true"> <DisplayStrings> <DisplayString ElementID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup"> <Name>Demo - Windows Server 2012 Health Service Watcher Group</Name> <Description>Contains Health Service Watcher for all instances in the Windows Server 2012 group.</Description> </DisplayString> <DisplayString ElementID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroupContainmentRelationship"> <Name>Windows Server 2012 Health Service Watcher Containment Relationships</Name> </DisplayString> </DisplayStrings> </LanguagePack> </LanguagePacks> </ManagementPackFragment>
4. Add a new empty management pack fragment named dis.WindowsServer2012HswGroup.mpx, paste the following code into it, and save the fragment. This fragment contains the actual discovery. The module performing the group population is specified in the data source. The main elements you need to be concerned with are highlighted; GroupInstanceId is the group (class) to be populated, MonitoringClass indicates what type of objects to populate the group with, and the expression indicates which source class (or group) to match. Also note MonitoringClass is AgentWatcher. This will populate the group with agents only, not other types of health service’s (like management servers or gateways).
<ManagementPackFragment SchemaVersion="2.0" xmlns:xsd="http://www.w3.org/2001/XMLSchema"> <Monitoring> <Discoveries> <Discovery ID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup.Discovery" ConfirmDelivery="false" Enabled="true" Priority="Normal" Remotable="true" Target="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup"> <Category>Discovery</Category> <DiscoveryTypes> <DiscoveryRelationship TypeID="MSIL!Microsoft.SystemCenter.InstanceGroupContainsEntities" /> </DiscoveryTypes> <DataSource ID="GroupPop" TypeID="SC!Microsoft.SystemCenter.GroupPopulator"> <RuleId>$MPElement$</RuleId> <GroupInstanceId>$MPElement[Name="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup"]$</GroupInstanceId> <MembershipRules> <MembershipRule> <MonitoringClass>$MPElement[Name="SC!Microsoft.SystemCenter.AgentWatcher"]$</MonitoringClass> <RelationshipClass>$MPElement[Name="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroupContainmentRelationship"]$</RelationshipClass> <Expression> <Contains> <MonitoringClass>$MPElement[Name="SC!Microsoft.SystemCenter.HealthService"]$</MonitoringClass> <Expression> <Contained> <MonitoringClass>$MPElement[Name="MWSL!Microsoft.Windows.Server.6.2.ComputerGroup"]$</MonitoringClass> </Contained> </Expression> </Contains> </Expression> </MembershipRule> </MembershipRules> </DataSource> </Discovery> </Discoveries> </Monitoring> <LanguagePacks> <LanguagePack ID="ENU" IsDefault="true"> <DisplayStrings> <DisplayString ElementID="Demo.HealthServiceWatcherGroups.WindowsServer2012HswGroup.Discovery"> <Name>Demo - Windows Server 2012 HSW Group Discovery</Name> <Description>Populates Demo - Windows Server 2012 HSW Group</Description> </DisplayString> </DisplayStrings> </LanguagePack> </LanguagePacks> </ManagementPackFragment>
Sign, seal, and import the MP to see the end result.
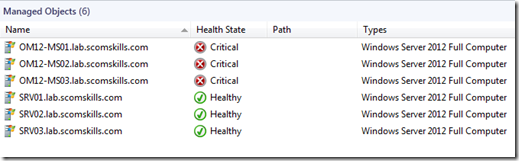
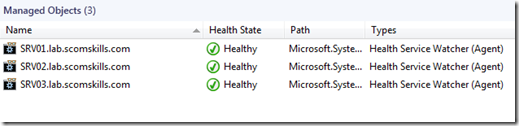
Source group contains a mix of computer objects – both agents and management servers.
The new group contains health service watcher instances for agents running on Windows Server 2012.
I plan to post more on creating groups using the Visual Studio Authoring Extensions in the future, so check back or subscribe to the RSS feed.
If you are still using the R2 Authoring Console, I have those examples posted here.